January 3, 2024

LastPass notified customers today that they are now required to use complex master passwords with a minimum of 12 characters to increase their accounts' security.
Even though LastPass has repeatedly said that there is a 12-character master password requirement since 2018, users have had the ability to use a weaker one.
"Historically, while a 12-character master password has been LastPass’ default setting since 2018, customers still had the ability to forego the recommended default settings and choose to create a master password with fewer characters, if they wished to do so," LastPass said in a new announcement today.
LastPass has begun enforcing a 12-character master password requirement since April 2023 for new accounts or password resets, but older accounts could still use passwords with fewer than 12 characters. Starting this month, LastPass is now enforcing the 12-character master password requirement for all accounts.
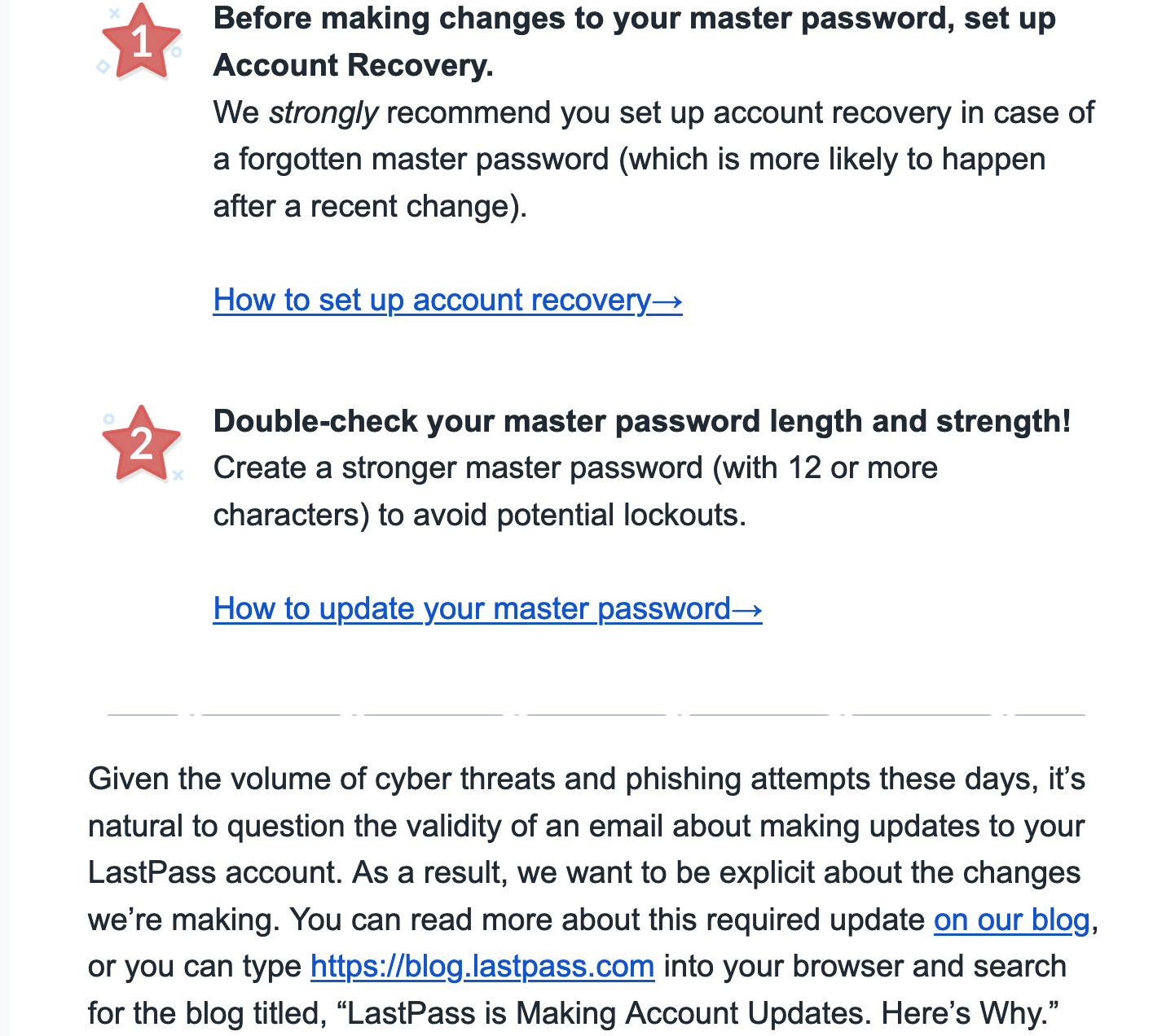
Furthermore, LastPass added that it will also start checking new or updated master passwords against a database of credentials previously leaked on the dark web to ensure that they don't match already compromised accounts.
If a match is found, the customers will be alerted via a security warning pop-up and prompted to select another password to block future cracking attempts.
As part of the same effort to increase account security, LastPass also started a forced multi-factor authentication (MFA) re-enrollment process in May 2023, which led to many users experiencing significant login issues and getting locked out of their accounts.
"These changes include requiring customers to update their master password length and complexity to meet recommended best practices and prompting customers to re-enroll their multi-factor authentication (MFA), among others," said Mike Kosak, a Senior Principal Intelligence Analyst at LastPass.
"Starting in January 2024, LastPass will enforce a requirement that all customers use a master password with at least 12 characters.
"Next month, LastPass will also begin immediate checks on new or reset master passwords against a database of known breached credentials in order to ensure the password hasn't been previously exposed on the Dark Web."