April 18, 2024 By Pierluigi Paganini
Russia-linked APT Sandworm employed a previously undocumented backdoor called Kapeka in attacks against Eastern Europe since 2022.
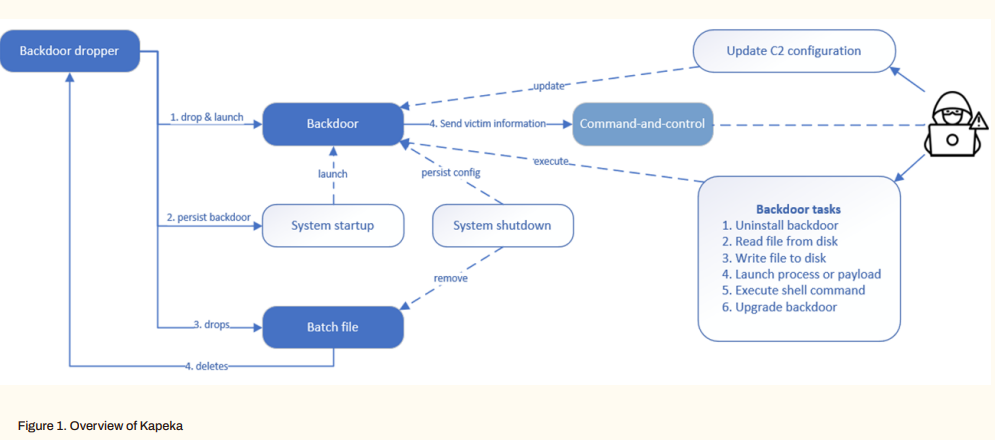
WithSecure researchers identified a new backdoor named Kapeka that has been used in attacks targeting victims in Eastern Europe since at least mid-2022. The backdoor is very sophisticated, it serves as both an initial toolkit and as a backdoor for maintaining long-term access to compromised systems. The nature of the targets, low detection rate, and sophisticated malware-supported features suggest that an APT group developed it.
WithSecure noticed overlaps between Kapeka and GreyEnergy and the Prestige ransomware attacks which are attributed to the Russia-linked Sandworm APT group. WithSecure believes that Kapeka is likely part of the Sandworm’s arsenal.
The Sandworm group (aka BlackEnergy, UAC-0082, Iron Viking, Voodoo Bear, and TeleBots) has been active since 2000, it operates under the control of Unit 74455 of the Russian GRU’s Main Center for Special Technologies (GTsST). The group is also the author of the NotPetya ransomware that hit hundreds of companies worldwide in June 2017. In 2022, the Russian APT used multiple wipers in attacks aimed at Ukraine,including AwfulShred, CaddyWiper, HermeticWiper, Industroyer2, IsaacWiper, WhisperGate, Prestige, RansomBoggs, and ZeroWipe.