This release consists of the following 79 Microsoft CVEs:
| Tag | CVE | Base Score | CVSS Vector | Exploitability | FAQs? | Workarounds? | Mitigations? |
|---|---|---|---|---|---|---|---|
| Windows TCP/IP | CVE-2024-21416 | 8.1 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-26186 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-26191 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Security Zone Mapping | CVE-2024-30073 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37335 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37337 | 7.1 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37338 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37339 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37340 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37341 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37342 | 7.1 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37965 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37966 | 7.1 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-37980 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Installer | CVE-2024-38014 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Microsoft Office SharePoint | CVE-2024-38018 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows TCP/IP | CVE-2024-38045 | 8.1 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows PowerShell | CVE-2024-38046 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Network Address Translation (NAT) | CVE-2024-38119 | 7.5 | CVSS:3.1/AV:A/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Network Watcher | CVE-2024-38188 | 7.1 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Web Apps | CVE-2024-38194 | 8.4 | CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Stack | CVE-2024-38216 | 8.2 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:L/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Mark of the Web (MOTW) | CVE-2024-38217 | 5.4 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:L/A:L/E:F/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Azure Stack | CVE-2024-38220 | 9.0 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Dynamics Business Central | CVE-2024-38225 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office Publisher | CVE-2024-38226 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Microsoft Office SharePoint | CVE-2024-38227 | 7.2 | CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2024-38228 | 7.2 | CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Standards-Based Storage Management Service | CVE-2024-38230 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Remote Desktop Licensing Service | CVE-2024-38231 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Network Virtualization | CVE-2024-38232 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Network Virtualization | CVE-2024-38233 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Network Virtualization | CVE-2024-38234 | 6.5 | CVSS:3.1/AV:A/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Role: Windows Hyper-V | CVE-2024-38235 | 6.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:C/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows DHCP Server | CVE-2024-38236 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Microsoft Streaming Service | CVE-2024-38237 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Streaming Service | CVE-2024-38238 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Kerberos | CVE-2024-38239 | 7.2 | CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Access Connection Manager | CVE-2024-38240 | 8.1 | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Streaming Service | CVE-2024-38241 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Streaming Service | CVE-2024-38242 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Streaming Service | CVE-2024-38243 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Streaming Service | CVE-2024-38244 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Streaming Service | CVE-2024-38245 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Win32K - GRFX | CVE-2024-38246 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Graphics Component | CVE-2024-38247 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Storage | CVE-2024-38248 | 7.0 | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:P/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Graphics Component | CVE-2024-38249 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Graphics Component | CVE-2024-38250 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Win32K - ICOMP | CVE-2024-38252 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Win32K - ICOMP | CVE-2024-38253 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Authentication Methods | CVE-2024-38254 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Kernel-Mode Drivers | CVE-2024-38256 | 5.5 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows AllJoyn API | CVE-2024-38257 | 7.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop Licensing Service | CVE-2024-38258 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Management Console | CVE-2024-38259 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop Licensing Service | CVE-2024-38260 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop Licensing Service | CVE-2024-38263 | 7.5 | CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop Licensing Service | CVE-2024-43454 | 7.1 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:H/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Remote Desktop Licensing Service | CVE-2024-43455 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Setup and Deployment | CVE-2024-43457 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Network Virtualization | CVE-2024-43458 | 7.7 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows MSHTML Platform | CVE-2024-43461 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Office Visio | CVE-2024-43463 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2024-43464 | 7.2 | CVSS:3.1/AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Microsoft Office Excel | CVE-2024-43465 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Office SharePoint | CVE-2024-43466 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | No | No | No |
| Windows Remote Desktop Licensing Service | CVE-2024-43467 | 7.5 | CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure CycleCloud | CVE-2024-43469 | 8.8 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Azure Network Watcher | CVE-2024-43470 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| SQL Server | CVE-2024-43474 | 7.6 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:L/A:L/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Admin Center | CVE-2024-43475 | 7.3 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:U/C:H/I:N/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Dynamics 365 (on-premises) | CVE-2024-43476 | 7.6 | CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:L/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Power Automate | CVE-2024-43479 | 8.5 | CVSS:3.1/AV:N/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Microsoft Outlook for iOS | CVE-2024-43482 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:N/A:N/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Mark of the Web (MOTW) | CVE-2024-43487 | 6.5 | CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:N/I:H/A:N/E:F/RL:O/RC:C | Exploitation More Likely | Yes | No | No |
| Windows Update | CVE-2024-43491 | 9.8 | CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Detected | Yes | No | No |
| Microsoft AutoUpdate (MAU) | CVE-2024-43492 | 7.8 | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
| Windows Libarchive | CVE-2024-43495 | 7.3 | CVSS:3.1/AV:L/AC:L/PR:L/UI:R/S:U/C:H/I:H/A:H/E:U/RL:O/RC:C | Exploitation Less Likely | Yes | No | No |
Security Update Guide Blog Posts
| Date | Blog Post |
|---|---|
| June 27, 2024 | Toward greater transparency: Unveiling Cloud Service CVEs |
| April 9, 2024 | Toward greater transparency: Security Update Guide now shares CWEs for CVEs |
| January 6, 2023 | Publishing CBL-Mariner CVEs on the Security Update Guide CVRF API |
| January 11, 2022 | Coming Soon: New Security Update Guide Notification System |
| February 9, 2021 | Continuing to Listen: Good News about the Security Update Guide API |
| January 13, 2021 | Security Update Guide Supports CVEs Assigned by Industry Partners |
| December 8, 2020 | Security Update Guide: Let’s keep the conversation going |
| November 9, 2020 | Vulnerability Descriptions in the New Version of the Security Update Guide |
Relevant Resources
- The new Hotpatching feature is now generally available. Please see Hotpatching feature for Windows Server Azure Edition virtual machines (VMs) for more information.
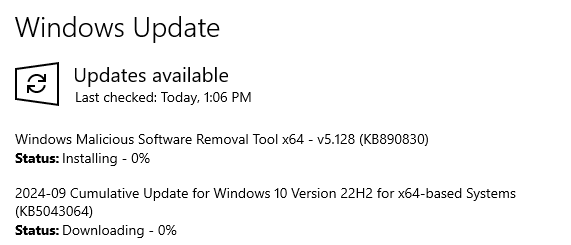
- Windows 10 and Windows 11 updates are cumulative. The monthly security release includes all security fixes for vulnerabilities that affect Windows 10 and Windows 11, in addition to non-security updates. The updates are available via the Microsoft Update Catalog. For information on lifecycle and support dates for Windows 10 and Windows 11 operating systems, please see Windows Lifecycle Facts Sheet.
- Microsoft is improving Windows Release Notes. For more information, please see What's next for Windows release notes.
- A list of the latest servicing stack updates for each operating system can be found in ADV990001. This list will be updated whenever a new servicing stack update is released. It is important to install the latest servicing stack update.
- In addition to security changes for the vulnerabilities, updates include defense-in-depth updates to help improve security-related features.
- Customers running Windows Server 2008 R2, or Windows Server 2008 need to purchase the Extended Security Update to continue receiving security updates. See 4522133 for more information.
Known Issues
You can see these in more detail from the Deployments tab by selecting Known Issues column in the Edit Columns panel.
For more information about Windows Known Issues, please see Windows message center (links to currently-supported versions of Windows are in the left pane).
| KB Article | Applies To |
|---|---|
| 5002624 | SharePoint Enterprise Server 2016 |
| 5002639 | SharePoint Server 2019 |
| 5002640 | SharePoint Server Subscription Edition |
| 5042881 | Windows 11, version 21H2 |
| 5043051 | Windows 10, version 1607, Windows Server 2016 |
| 5043064 | Windows 11 version 24H2 |
| 5043067 | Windows 11, version 21H2 |
| 5043076 | Windows 11, version 22H2, Windows 11, version 23H2 |
| 5043080 | Windows 11 version 24H2 |
| 5043083 | Windows 10 |
| 5043087 | Windows Server 2008 (Security-only update) |
| 5043135 | Windows Server 2008 (Monthly Rollup) |
Released: Sep 10, 2024